Today, the arms race has shifted from better ways of creating ever-more-dangerous bombs to better ways of bypassing digital security. Much like the nuclear focus from before, however, one of the main adversaries in this ring is Russia, whose efforts to infiltrate digital databases have extended everywhere from political organizations to power plants — all the while proving as effective as they are elusive.
Still, government intelligence from around the world has been able to track and identify many of these Russia-originating threats. In the process, these agencies have uncovered both the identities of these groups and their most common methodologies for cyberattacks.
Now that Russia has made physical incursions on the world, it can’t be understated how vital it is for digital communications experts to understand how these groups operate. To keep yourself safe, it’s all the more important you know what threats are out there.
Snake
One of the foremost figures in the Russia-based digital rogue’s gallery, Snake is a hacking collective believed to have been in operation since 2004. The association is considered by Germany’s Federal Office for the Protection of the Constitution (BfV) to be “the Holy Grail of espionage” and is given the highest possible ranking on the Advanced Persistent Threat (APT) index.
The first known attack by Snake was conducted in December 2017, when malware infecting the German Foreign Ministry began commanding their computers to contact spoofed websites. This allowed Snake to collect data from the ministry’s servers and access classified documentation.
Fortunately for investigators, however, the cyberattackers left two usernames in the hacked databases: “Vlad” and “Urik,” which despite their vagueness, proved to be enough of a lead to trace the attacks back to the Russian company Center-Inform. Since Center-Inform has known ties to Russia’s Federal Security Service (FSB), intelligence communities around the world have largely concluded that Snake operates as a Russian state-sponsored cyberattack group.
Both the German BfV and the Canadian signals intelligence agency CSE describe the malware created by Snake as “genius” in design. This praise mainly speaks to how effective the malware is at conducting actual cyberattacks: once it’s infected a computer, it takes very little effort or expertise for a hacker to use it for illicit data collection.
Of course, that’s only the case if devices get infected at all — but as other examples show, that initial infection doesn’t always come from a forced entry into systems.
Fancy Bear
If you paid much attention to American politics circa 2016, this name may already be familiar to you. Fancy Bear, also known as APT28 or Sofacy, exploded into the mainstream after being linked to the cyberattacks conducted on the Hillary Clinton presidential campaign, the Democratic National Committee and the Democratic Congressional Campaign Committee in 2016. However, the group is believed to be responsible for other attacks between 2014 and 2018 on high-profile entities, including the World Anti-Doping Agency, the Organization for the Prohibition of Chemical Weapons and the Spiez Swiss Chemicals Laboratory.
Fancy Bear’s targets aren’t limited to the United States and western Europe — or even to organizations. Other notable victims of the group’s cyberattacks include journalists from Russia, Ukraine and Moldova who wrote critically about Vladimir Putin. Between 2014 and 2016, amid Russian incursions on Ukraine and Crimea, cyberattacks associated with Fancy Bear even hit Ukrainian artillery units and rendered them inoperative.
The targets of Fancy Bear being largely those within Russian state interests, it’s easy to assume they’re associated with the Kremlin. But more definitively, investigations carried out by the cybersecurity firm CrowdStrike, the UK’s Foreign and Commonwealth Office and the US Special Counsel have linked Fancy Bear to the Russian government and Russia’s GRU intelligence agency.
What makes Fancy Bear stand out among cyberattackers is its methodology. The group typically obtains its data not through forced infiltration but through social engineering: It creates websites that deceive users into inputting confidential data, and many of its campaigns have been the result of phony communications that trick recipients into providing login credentials (known as “phishing” or, in the case of targeting one important person or account, “spear phishing”). Once targets click on these websites or input their credentials, Fancy Bear will infect a device with software that illicitly collects data from the device itself and the adjoining network.
Fancy Bear is quite effective at what it does, even capable of carrying out multiple hacking campaigns simultaneously. However, it’s far from the only Russia-associated group to use such techniques.
Cozy Bear
Another Russia-linked entity known to make heavy use of phishing is Cozy Bear, also called APT29 or The Dukes. In operation since at least 2008, Cozy Bear is believed to be associated with Russia’s Foreign Intelligence Service (SVR) and targets government networks throughout Europe, especially NATO member nations. Other targets of the group include think tanks and, reportedly, the Democratic National Committee in the United States.
Cozy Bear’s most impactful cyberattack came in 2020 with the massive SolarWinds data breach. SolarWinds, a technology firm in the United States, was covertly infiltrated by Cozy Bear affiliates to plant data-gathering malware in the company’s main system. This hack soon spread to thousands more victims as SolarWinds unknowingly distributed the altered code via a patch update — passing the exploit onto major customers, including Microsoft, Intel and the US Department of Defense.
Like Fancy Bear, Cozy Bear uses spear-phishing as its primary means of entering systems, with enormous campaigns attempting to solicit credentials from major figures in target organizations. The group is known for dogged persistence in these efforts as well and will typically launch fresh efforts against established targets if access is shut off.
Sandworm
While this group is often known by its Dune-referencing name, it’s also called Voodoo Bear in some circles (apparently, someone in cybersecurity quite enjoys an ursine naming convention). But whatever name the group is given, Sandworm ranks among the most infamous of Russia-linked cyberattackers.
Reportedly associated with GRU, the group carried out the single most extensive cyberattack in history with its NotPetya malware attacks, which in 2017 simultaneously hit France, Germany, Italy, Poland, the UK, the United States and especially Ukraine, costing the victims a combined $10 billion in damages.
In more recent efforts, Sandworm has developed malware called Cyclops Blink, which malicious agents have placed on network devices produced by the IT security vendor Watchguard. According to US intelligence agencies, Cyclops Blink is likely a successor to Sandworm’s own VPNFilter program; years earlier, VPNFilter infected network routers and spread to half a million machines, turning them into a global botnet controlled by Sandworm and, by extension, the GRU.
But, what was the ultimate goal of VPNFilter? Or, for that matter, of Cyclops Blink? Concerningly, we don’t actually know. As likely as it is that Sandworm has installed this malware for surveillance purposes, it’s just as possible that they’re setting up a digital infrastructure for covert Russia-originating communications. Similarly, the reason could be to lay the groundwork for a massive disruption of affected networks — it’s worth remembering, after all, that Sandworm was able to take down significant parts of Ukraine’s electrical grid in 2015.
The good news is, in the case of Cyclops Blink, Watchguard successfully patched the vulnerability Sandworm used for entry, and users can wipe the malware by clearing their machines and reinstalling the software. However, the example still illustrates that personal hardware can be made into unwitting tools for cyberattacks.
Best Practices & Lessons Learned
As shadowy and unstoppable as all of these groups want to be seen as, the fact remains that none of their methodologies are a guaranteed means of entry. Even when skilled cyberattackers lurk online, a combination of best security practices and smartly designed software is bound to keep you safe.
Chief among these best practices is to be educated against phishing attempts. This means not clicking suspicious links, not responding to spam emails and never replying to messages with your login credentials or account recovery info. Just by steering clear of shady websites and files, you’ll be keeping yourself fairly safe, but you should also consider further securing any important accounts with two-factor authentication or single sign-on.
In terms of system infrastructure, moving from on-premises hardware to the cloud will also offer significantly improved online protection. Consider how often cyberattackers have used malware and exploits in hardware to carry out their efforts: when a system moves to the cloud, this risk is largely mitigated, both because vulnerabilities are patched as soon as the associated hotfix is deployed and because there’s no longer any traditional “hardware” to infect.
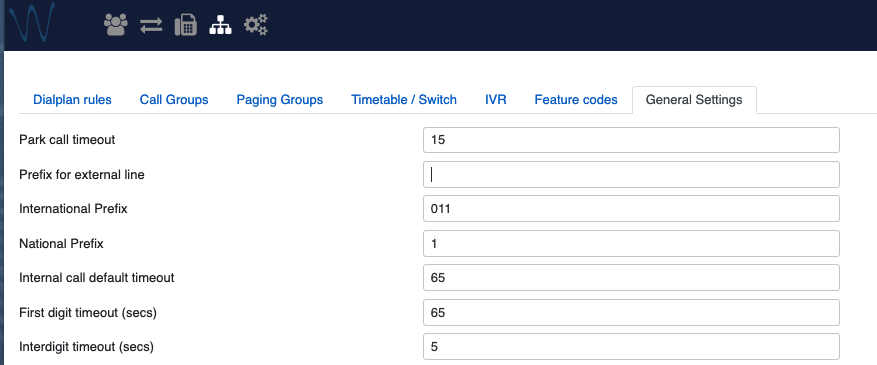
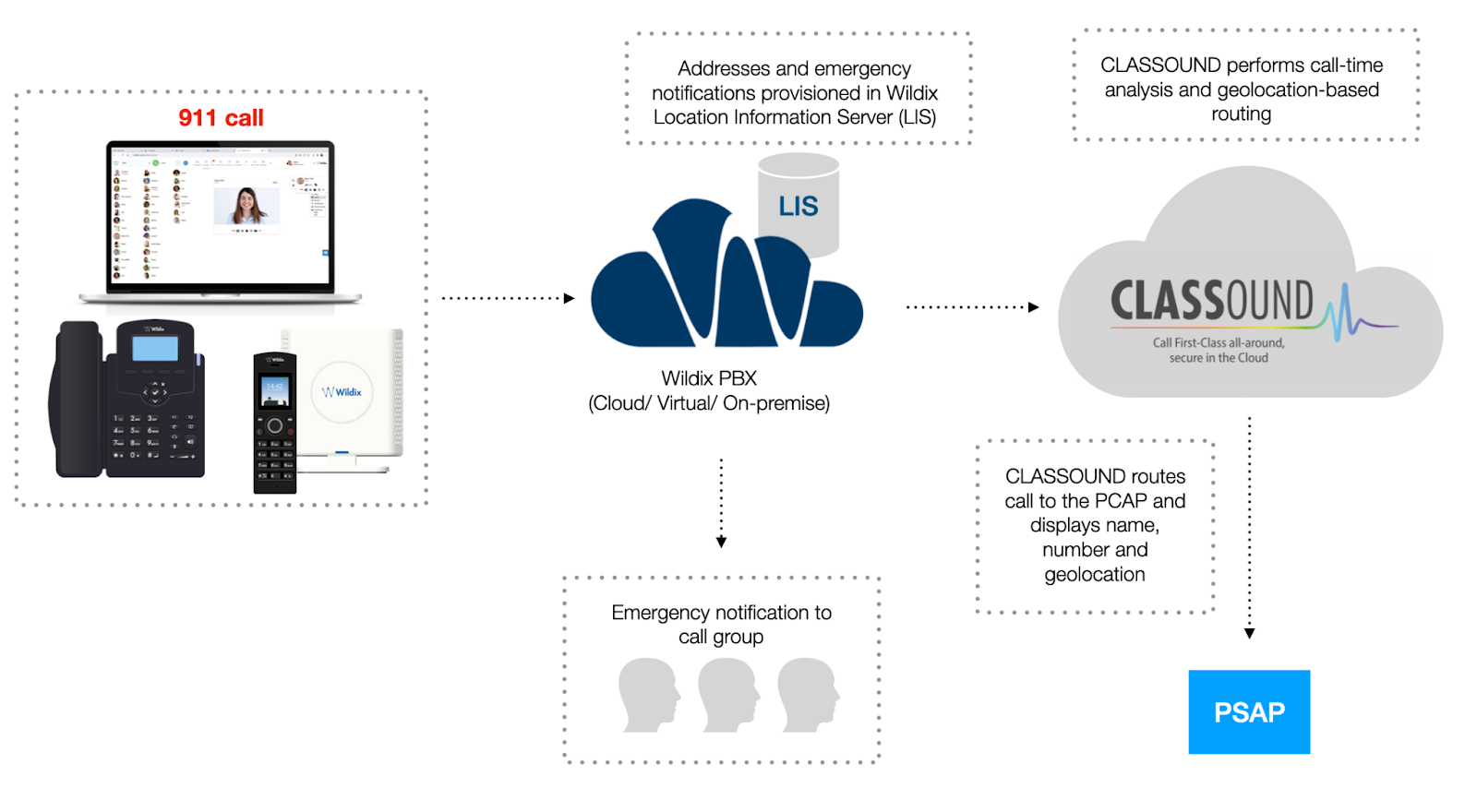
More broadly speaking, of course, it still pays to be using a system that itself utilizes smart security protocols. As far as digital communications are concerned, Wildix distinguishes itself with a structure that’s fully secure by design thanks to a combination of technologies that protect users from infiltration and eavesdropping without VPNs, SBCs or other add-ons. You can read more about Wildix’s security practices in our free white paper.
However you choose to operate, doing so in full security has never been more crucial. As Russia encroaches on Ukraine, they’re likely to relaunch cyberattacks with renewed force — likely roping foreign hardware into their efforts in the process. If you’re looking for some way to work against these war efforts, it truly can start with understanding Russia’s most common methods of cyberattack and keeping your devices safe against them.
For more tips on cybersecurity and digital safety, subscribe to receive our magazine for free!